The worst call/email to receive, as a sysadmin, is that users are reporting their files “looking funny,” only for you to see your client’s file server was hit with ransomware. You start saying a prayer hoping your backups that ran overnight were successful, as you send an email to your administration to begin the recovery process of the malware-infected server.
When was the last time you assessed your company’s infrastructure? What do we have in place to make sure this doesn’t become a trend in your environment? What knowledge have we equipped our end-users to be the front-line defense when it comes to such malicious attacks? Here are a few pointers to help start assessing your environment.
1. Is your employee staff trained on phishing attacks?
a. Keeping your employees up to speed on the latest phishing attacks, along with training, can be imperative to your success in preventing malicious attacks. A great source for anti-phishing and free training can be found here. https://resources.infosecinstitute.com/category/enterprise/phishing/phishing-countermeasures/top-16-anti-phishing-resources/#gref
2. Network segregation
Segregating your network (DMZs, VLANs/etc.) can help reduce the risk of data loss in the event of an attack. Knowing what assets are mission-critical and most vulnerable allows you to identify the best solution for your company’s preventative strategies against attacks.
3. Where are your backups being stored?
With cloud backup services becoming more affordable and secure, having different areas where data is stored is imperative in today’s Big Data environments. Finding a hybrid backup solution that fits your everyday business needs will ensure, in the event of a ransomware attack, that your data can promptly be recovered.
4. Use reputable antivirus software and a firewall
Keeping your network infrastructure protected is another line of defense that you should not “cheap” out on. Spend time researching the most optimal hardware and software for your environment so you can rest easy that your network is protected. Look at the expense as an investment. Spending 3k on hardware and licensing on priceless data that can be taken away in an instant may have you change the way you think about the cost.
5. Don’t give regular users administrative rights on their workstations.
The last thing you want to happen is an end-user disabling or removing security functions or features from their workstations that can cause any malicious activity to exist. Granting admin rights can and will allow this to happen eventually.
6. Disable smb v1- This can be done by either PowerShell (Disable-WindowsOptionalFeature -Online -FeatureName smb1protocol) or through Server Manager>Add/Remove Features (See screenshot)
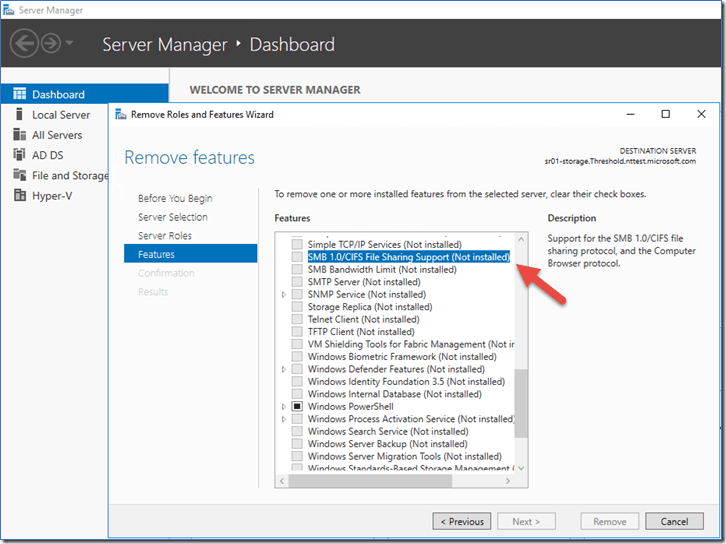
This will help prevent common ransomware like WannaCry from spreading across your whole network.
7. Limit user access to shared drives
In Windows, set proper NTFS permissions management via security groups. Since ransomware can encrypt only the files the victim has access to, a strict least-privilege model limits the damage it can do.
8. Enable secure passwords and account “lockout policies”
Protect your on-premises and virtual environments to reduce the chance of ransomware infection after a brute-force attack. To learn more about how to create on lockout policy, click here.
9. Do employ content scanning and filtering on your mail servers.
Content scanning your incoming email traffic is a critical first line of defense to your environment. Emails are the number one intrusion method for most malware/ransomware attacks through phishing emails. Having a strong filter in place will negate this.
10. Do make sure that all systems and software are up-to-date with relevant patches.
Keeping your systems Operating systems updated is another crucial step in protecting your environment. Security patches are implemented whenever new security definitions and vulnerabilities are found, so ensure you are keeping your infrastructure up to date.
11. Do not provide personal information when answering an email, unsolicited phone call, text message, or instant message.
If you have any feeling that something is not right, tell someone. It is better to have an expert review the contents than just assuming and causing an infrastructure catastrophe.
12. If traveling, make sure you use a trustworthy Virtual Private Network (VPN) when accessing public Wi-Fi.
Going to Starbucks for free wifi isn’t the greatest idea when it comes to security; however, sometimes it is a must. Having a VPN allows your data traffic to be secure in this kind of situation.
13. Do not pay the ransom.
Think about it. Someone you don’t know has your data encrypted. They have already shown malicious intent. Paying the ransom to someone like this is like playing “rush and roulette”
14. Restore any impacted files from a known good backup.
Restoring files from a backup solution is the fastest way to get your data back and get your environment back to normal operations.
Using third-party solutions, such as VEEM, Azure, or Barracuda, use cloud solution applications that allow you to restore flat files or BMR (bare metal restores), giving you an edge over these malicious attacks.
Need help with managing your infrastructure? Contact XTIVIA today so you can rest assured your environment is safe.